the ingenuity
IT consulting
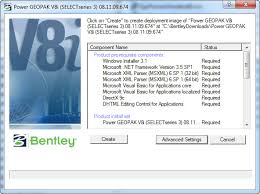
 IT consulting refers to the widest range of solutions designed to optimize existing IT resources for the needs of a particular business, its structure and features. Ultimately, its goal is to improve the operation of management systems and office equipment available at the enterprise for the benefit of the business. High-quality and versatile consulting includes:
IT consulting refers to the widest range of solutions designed to optimize existing IT resources for the needs of a particular business, its structure and features. Ultimately, its goal is to improve the operation of management systems and office equipment available at the enterprise for the benefit of the business. High-quality and versatile consulting includes:
IT audit
optimization of existing ones and development of a strategy for introducing new IT solutions;
audit of business processes with various penetration depths.
It is unlikely that anyone today will seriously deny the serious role of IT processes in running a business, especially a large one. At the same time, the larger the business, the more difficult IT solutions will be Continue reading
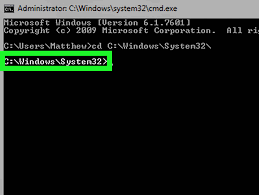
How hackers turn our printers, cameras and thermostats into sinister cyber army
 In the fall, several large hacker attacks took place in which IoT devices were used. One of them is for Russian banks. The Daily Poster tells the story of other interesting hacks and explains how attackers harm people through light bulbs and refrigerators.
In the fall, several large hacker attacks took place in which IoT devices were used. One of them is for Russian banks. The Daily Poster tells the story of other interesting hacks and explains how attackers harm people through light bulbs and refrigerators.
Internet of things attacks Russian banks
On Thursday, November 10, five large Russian banks were subjected to DDoS attacks – a large number of junk requests came to sites that loaded servers and made sites inaccessible. The attacks went to the Moscow Exchange, Alfa Bank, Sberbank, Otkritie Bank, VTB Bank and Rosbank. Almost all banks managed to cope with the load. Among the possible organizers of the attack was a hacker under the nickname vimproducts, whose customers were allegedly dissatisfied with Russia’s interference in the Continue reading
Apple iPhone OS
 Preamble: Recently, all sorts of mobile and, especially fashionable, cloud technologies have captured the attention of mankind. Desktops and laptops faded into the background, giving way to more compact and attractive toys for leisure and business. Our new friends not only know how to polyphony, show pictures and surf the Internet, but also become fashion accessories that cannot be put on a table in a cafe next to a cup of tea, from time to time sliding the index finger on the inscription “Slide to unlock”. But the day is heading towards the evening, your electronic partner is tired and he has to go on a charge. Well, insert the USB tail where necessary … let it rest. Continue reading
Preamble: Recently, all sorts of mobile and, especially fashionable, cloud technologies have captured the attention of mankind. Desktops and laptops faded into the background, giving way to more compact and attractive toys for leisure and business. Our new friends not only know how to polyphony, show pictures and surf the Internet, but also become fashion accessories that cannot be put on a table in a cafe next to a cup of tea, from time to time sliding the index finger on the inscription “Slide to unlock”. But the day is heading towards the evening, your electronic partner is tired and he has to go on a charge. Well, insert the USB tail where necessary … let it rest. Continue reading