tanya
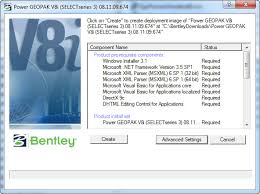
How to protect a site from hacking by a hacker
 With an insecure site, many troubles can happen: hacking by hackers, attacks, virus infection. Some of the most common attacks:
With an insecure site, many troubles can happen: hacking by hackers, attacks, virus infection. Some of the most common attacks:
XSS attack. The virus code is embedded in the data sent by the user (in the unprotected fields of the registration form, subscription, order, call back, comment). A knowledgeable user can thus “break” the site, making it inoperative.
SQL injection. An action is added to the SQL query that was not originally there, without violating the structure of the previous query. This allows you to access databases, modify and download files from Continue reading
Rules of work and behavior on the Internet
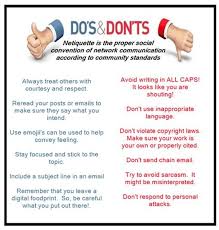 Every Internet user should be clearly aware that the Internet can not only benefit, but also cause considerable harm. To avoid trouble, strictly follow the recommendations and rules listed below.
Every Internet user should be clearly aware that the Internet can not only benefit, but also cause considerable harm. To avoid trouble, strictly follow the recommendations and rules listed below.
• To use the Internet safely, you must have a good antivirus program. At the same time, it is necessary that the installed antivirus can work in monitoring mode – this will allow you to identify a danger immediately when it occurs.
• Use extreme caution when visiting unknown resources on the Internet. Currently, viruses and malicious programs have spread, for infection with which it is enough just to visit a specific web page.
• If you are connected to the Internet through a telephone line, the modem speaker must be turned on. This will Continue reading